Blockchain technology is one of the most trending technology nowadays. All big firms like Google, Microsoft, Amazon, Facebook, Walmart and many more are hiring blockchain developers to work on this technology.
Blockchain technology was first introduced by Bitcoin back in 2009 and over the last 10 years, Blockchain has evolved to new levels. Bitcoin blockchain keeps records of each and every transactions made on the network from 2009 to today.
When you try to learn more about Blockchain technology you may encounter the words “distributed, decentralized, public ledger”.
In this article, we are going to explain what is Blockchain technology? What makes blockchain different from the other available technologies? Some advantage and disadvantages of blockchain and the applications where blockchain can be used. If you are a developer than learning Blockchain is a must skill to make good money.
Table of Contents
- What is Blockchain?
- Public and Private Blockchain
- How Blockchain Works?
- Is Blockchain Secure?
- Possibility of Blockchain Hack
- Blockchain and Bitcoin
- Advantages of Blockchain
- Disadvantages of Blockchain
- Practical Application Using Blockchain
- Scope of Blockchain
1 What is Blockchain?
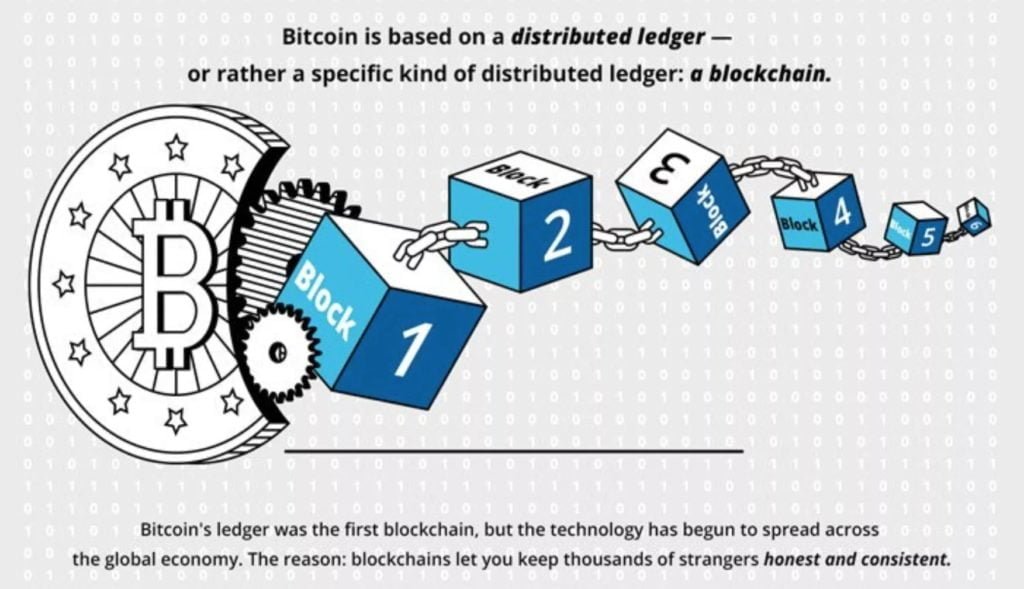
The names Blockchain itself explains a lot. Blockchain means a chain of blocks where each block can contain some data. All blocks are connected in a chain by some hashing algorithm.
Blocks on the blockchain contain digital information and have mainly three parts:
- Blocks stores all information about the transactions like time, date and the amount (any currency) of the purchase. Let’s say that its a record of all your recent purchases from Amazon or any other e-commerce website (it is just an example Amazon is not using blockchain to keep records of orders and transaction).
- Blocks store information about who is participating in the transactions. For example, if you are buying something from a store, block store your information and the store information together (in the form of digital signature), if the blockchain is public then the transaction is visible to everyone and if it is a private blockchain only the store and you can see the transaction. We will discuss public and private chain later in this post.
- Blocks stores information that distinguishes them (blocks) from each other. Just like you and me have different names, all blocks contain a unique code called “hash” that shows this block is different from other blocks. Your transactions may store in a single block or in multiple blocks depends upon the architecture of blockchain used and the time of the transactions.
Here we have just used the example of a single purchase from Amazon but the reality is different there are daily a hundred of thousands of transactions on the e-commerce website. Each block has a size limit (say 1 MB) and depending on the size of each transaction, only a few thousands of transactions can be stored in a block.
2 Types of Blockchain
There are 2 types of Blockchain networks:
Public Blockchain
Public Blockchain networks are available for everyone to view the transactions on the chain, run a node, contribute to the Blockchain code as developer etc.
Public Blockchains are fully decentralised and the record of all transactions (blocks) are stored on multiple computers (nodes) all over the world. This makes that any change in the blockchain record is quite impossible because attackers need to change the data in all nodes of the blockchain. That is much time and money consuming process.
The best example of public Blockchain is: Bitcoin
Private Blockchain
A private blockchain network is not available for everyone. Only an authorised person can see the transactions and data of the blockchain. The blockchain network is also maintained by some central authority. The central authority will verify all the blocks before adding the block to the network.
The control of the network is in the hands of some people and they may reject a transaction if found suspicious. A private blockchain is more centralized as compared to the public blockchain.
Example of Private blockchain are: Ripple and a central bank blockchain
3 How Blockchain Works?
Now a question rise in your head that how these blocks are connected to each other and how blockchain stores all data? We are going to explain how blockchain works and how all blocks are connected to each other.
Below is a simple explanation of how blockchain works and adds new blocks:
- Let’s take an example of your Amazon purchase, first, you need to select a store/product and then enter your details like address, then you need to check out the purchase.
- The transaction is made and must be verified to complete the purchase. It’s like a library needs a librarian to keep track of all books and manage them in a sequence. In Blockchain the librarian job is left up to a network of computers. A Blockchain network may consist of a thousand of computers (Bitcoin Blockchain has 5 million) spread across the globe (if this is a decentralised Blockchain). When you make a transaction you need to pay a little fee to the network to verify the transaction, all computers on the Blockchain network are now in a race to verify the transaction and who confirms the transaction first gets the fee (nodes takes a fee to secure the network). The network checks the transaction time, amount and participates and after verification add the information to a block.
- After the transaction information verified as accurate, it gets the green light to add into a block. The transaction amount, time, your digital signature and Amazon digital signature are added into a block and the block is ready to meet another hundreds/thousands of blocks like this.
- As we have explained earlier in the post, a block can consist of more than one transaction (the number goes to few thousand as depends on the size of the block) when all transactions in a block are verified then the block gets a unique identification code called a hash. The block has also given the hash of the recent block so that the blocks can be added into the Blockchain.
The block is now added to the Blockchain and is now publically available for everyone to view the information it contains (all the transactions). Check Bitcoin Blockchain, here you can find all the information time, amount, block position in Blockchain, and by whom the block is verified and added to the Blockchain.
4 Is Blockchain Fully Secure?
Is Blockchain fully secure to save all the information about a transaction? Let’s explore 🙂
Always new blocks were stored linearly and chronological order. That is, new blocks always added at the end of Blockchain, if you look at Bitcoin Blockchain you can see each block position on the chain, called “height”.
Once a block added to the Blockchain, it is very difficult (not impossible) to alter the contents of the block. As we discussed earlier each block has a unique hash, connected with the previous block hash. Hash codes are created by a math function that converts all information into a string of numbers and letters. If anything is changed in the information the hash value changed and blockchain rejects the block.
Let takes an example that Naveen wants to send $1000 ( or 0.1 BTC) to Monty for a service than the hash will be looks like:
786A832913348D9BB6E35ABF60CB451934F58A9E648CA2E28724A04AACEEBB6C
Now if Naveen plays over-smart and change the amount to $500 (0.05 BTC), then the whole hash value is changed and the block will be rejected by the blockchain network. The new hash looks like:
E69CC8EF3A3B3D569C6DCE67445B3699C3B01FDE588C27ED4AF34DCDAAC8D774
Even if you change a single letter to uppercase or lowercase the whole hash value changed.
If a hacker wants to change your data or any information on the blockchain, he/she need to change the entire blockchain network which requires a lot of computational power and time-consuming.
When a hacker tries to edit any information of the transaction, the block hash will be changed and as we discussed above every block contains the hash of the previous block. So what happens here is the next block contains the hash of the block hacker wants to change or edit the transaction information, so if the hacker wants to clear his tracks and the block will be accepted by Blockchain he needs to change the hash of the next block also. This process goes on until the hacker changes the hash of all blocks, this will takes a lot of computational power and energy (money).
As we said earlier in this post changing data in the blockchain is not impossible but the hacker needs to change and recalculate the hashes of all blocks that require an enormous amount of computational power that is quite impossible to acquire.
A public blockchain (decentralized) is a trustless system, there is no central authority to validate the transactions. Anyone can add a block (transactions) and validate the transactions on the blockchain network that must pass a test called “consensus models”. Bitcoin network uses the Proof-of-Work (PoW) system.
5 Possibility of Blockchain Hack
As we discussed above the working of the blockchain network, you will learn that the data is stored and maintained by public nodes (users). All the nodes must be agreed with others that the data is correct and added to the blockchain. Whenever a user joins the blockchain network, a full copy of the blockchain (data/transactions) is downloaded on the computer and verified form the other nodes.
What happens if a node data is different from other nodes? The data is manipulated maybe by human/machine errors or by some hacker.
Blockchain technology is designed in a way that it does not allow the existence of multiple blockchains through a process called “consensus”. If there are multiple copies of blockchain exists with different data then the consensus protocol will adopt the longest chain of the network. Here longest chain means that more nodes have the same blockchain and will add new blocks into it. The consensus protocol is a strength of blockchain technology as well as weakness.
51% Attack on Blockchain
A hacker can take advantage of the longest chain adoption rule. The attack is known as the 51% attack. Let’s take an example of the bitcoin blockchain that has 5 million computers (we are taking here round figure that is easy to divide), so to make the longest chain hacker need to control at least 51% of the total computers connected to bitcoin network that is 2.5 million and one more. Now the hackers have full control over the bitcoin network and can spend bitcoin via a transaction and then reverse it that gives all nodes the data that they still have the coins in their wallet this is called “Double Spending”. Double sending will allow users to spend the same coins over and over again. Bitcoin is made to fight the double spending of banks.
The 51% attack is very difficult to execute the bitcoin network because the hacker needs to control millions of computers that are distributed across the globe. The 51% attack was possible back in 2009 when Bitcoin was founded and only have a few computers connected to the bitcoin network, but at that time bitcoin has no value so it is not profitable to execute a 51% attack on bitcoin.
User fear of 51% attack limit monopolies to control the network. One of the Bitcoin mining pools Bitfury has pooled thousands of high specifications computers together to take control over the bitcoin blockchain. At that time Bitcoin was valued $700 each coin.
In March 2014, Bitfury positioned itself to take control of more than 50% of total computers of the bitcoin network, however instead of continuing to increase their computational power Bitfury decide to self-regulate the power and vowed that they never go above 40%. Bitfury sense that if they continue to increase their power and obtain more than 51% power, bitcoin may see a rapid selloff from the users because of fear and bitcoin will not be valuable anymore. In other words, the whole blockchain system depends on the faith in the blockchain network, if users lose the faith in bitcoin network the information stored on it is worthless and bitcoin becomes useless. Now everyone knows that if they increase their computational power to a point they will start losing money because of heavy selloff.
At the time of publishing this article (9 September 2019), Bitfury has a 2.3% share of total computing power on the bitcoin network.
6 Bitcoin and Blockchain
The concept of blockchain is simple: gathers digital information into blocks and let everyone access the data stored on the blockchain. It is a little difficult to understand without seeing the technology in action. Let’s see how the first application of blockchain: Bitcoin works.
Blockchain technology was first introduced by Stuart Haber and W. Scott Stornetta in 1991, two researchers who wanted to build a system where the information in documents is timestamped and cannot be altered. It takes almost two decades to implement the technology in a real-world application.
Bitcoin was the first to use the blockchain technology. Bitcoin blockchain was launched in January 2009 by Satoshi Nakamoto (the real identity was never revealed). The creator of Bitcoin referred to it as “a new electronic cash system that’s fully peer-to-peer, with no trusted third party.”
People all across the world have an interest in Bitcoin and cryptocurrency. According to a report by the Cambridge Centre for Alternative Finance, 5.9 million people all across the globe have Bitcoin. The report was old from 2017 and the number may exceed 10 million now.
Now if the 5.9 million people want to spend Bitcoin on buying and selling of services or want to buy something from the website that accepts Bitcoin (BTC). This is where blockchain comes into play.
When you buy or transfer from fiat currency or cash, the payments are verified by a central authority, usually a bank or government. But Bitcoin is not controlled by anyone, Bitcoin is fully decentralized. The transactions made by the Bitcoin network is verified by a network of computers called ‘Miners‘.
When a payment is made via Bitcoin, all the computers on the bitcoin network race to verify the transaction. To verify the transaction, a program is run onto the computers to solve the complex mathematical problem and generate a ‘hash’, we have already discussed how hash generated and stored into blocks above in this post. The transaction is now verified and put into a block and the transaction data is now visible to all and cannot be altered.
In the case of Bitcoin and almost all blockchain networks, the computer that successfully verifies the transaction (block) and generates a hash code will be rewarded for their work in cryptocurrency tokens (for Bitcoin in BTC). This process of verifying a block on Bitcoin blockchain is called Bitcoin Mining.
All the blocks are visible publically, check Bitcoin blocks here. Bitcoin blockchain does not show all the data of users like name, address, bitcoin chain only shows bitcoin addresses and amount associated with them. A bitcoin address is just like a bank account number on which you can receive BTC.
To conduct any transaction on the Bitcoin network, the user must need a Bitcoin wallet. Bitcoin wallet sends and receives BTC from any other Bitcoin wallet. A bitcoin wallet consists of two keys: Public Key and Private Key. Public Keys are used to receiving BTC from any other Bitcoin wallet and will be publically visible to everyone on the Bitcoin chain. The private key is used to generate a unique digital signature for every user.
7 Advantages
Blockchain has many advantage over the traditional ways to store information. The data is stored in blocks and all the nodes on the network keep the record of the blocks. User privacy, low processing fee, the strength of network and insurance that the data is not manipulated are some of the main advantages of blockchain. Some advantages are given below:
- High Accuracy
- Low Cost because of Third-Party Removal
- Decentralized Network Makes it Hard to Hack
- Efficient Network
- Transactions are Publically Visible
- Provides Privacy and security
High Accuracy
All transactions on the blockchain network are verified by thousands or millions of computers all across the globe. This eliminates all human involvement in the verification of transactions so results in higher accuracy. However, if a computer/node makes a mistake and downloads the wrong copy of data that will not be spread to all nodes until the same wrong copy will found on more than 51% of total computers. As we discussed above the 51% attack is not profitable and is quite impossible to execute.
Low Cost
Whenever you make a transaction via bank, you need to pay the bank a fee to verify your transaction. Here the bank is a third party between the sender and receiver and takes its commission. Almost everything is now verified by third parties and they make money. As we discussed above in a blockchain network all transactions are verified by a network of computers. There is no central authority to take the fee however miners take a small fraction of fee in the same token/currency to verify the transactions. Even users can select the priority of the transaction and pay less fee for fewer priority transactions. Bitcoin network has a very low fee start from $0.1 to $2.
Decentralized Network
Blockchains does not store the information on a central location. Each node/computer that is connected to the blockchain network anywhere from the world has the full copy of all the transactions. That makes it difficult to hack and change any information. If a hacker wants to change any information or transactions, he must need to change the blockchain data of more than 51% computers that are connected to the network. Whenever a new block added to the blockchain all the nodes connected to the network needs to update their copy of the blockchain.
Efficiency
When you make a transaction via any traditional methods say banks there is a central authority that verifies all the transactions. If you submit a deposit check on Friday evening the funds will arrive in your account after 2-3 days on Monday. Central authorities only operate five days work in a week and only in business hours whereas blockchain works 24*7. Transactions on a blockchain network are confirmed within a few minutes (or in seconds depends on the network type) and considered secured after few confirmations (in case of Bitcoin 6 confirmations ensures that the transaction will not be changed or altered). Blockchain transactions are useful for the cross border where multiple third parties are involved and take a high fee. Time zone difference is also an issue for traditional transactions.
Transparency
All the transactions are publically visible on the blockchain. The transactions show date, time, amount and wallet addresses of the participants keeping their personal information hidden. Added to this blockchain technology is open source and anyone can see the code and contribute for its development. When you want to add any new feature of change code the majority of the network will support your work for implementation. Blockchain uses decentralized voting system to add or remove any features.
Privacy and Security
As we discussed all the is stored in to blocks and visible to everyone on the network but the personal information is hidden. You can only see the transaction history of an address but you never knew the identity behind the address (exception: the person is using a third-party wallet that requires KYC). Many people misunderstand that Bitcoin is anonymous, Bitcoin is pseudo-anonymous because it shows everything about a transaction except personal identity. It’s same as when a bank hacks all the data and information of users is compromised.
Blockchain provides full security and no one can change or alter the transactions. Whenever anyone makes a transaction, thousands or millions of computers connected to the network rush to confirm the transaction to take the confirmation fee. The transaction copy is saved in all the computers that are connected to the network if a copy is changed or altered by any ways other computers reject the node and force it to download the real copy (majority copy).
8 Disadvantages
As every emerging technology have some limitations, blockchain has also some road barriers. There are not only technical limitation but also political and adoption problem with the technology. Technical limitations are easy to solve than political and regulatory problems. These are some disadvantages:
- Network Maintenance Cost
- Transaction Speed
- Illegal Activities
- Hack Possibility
- Regulatory Problems


