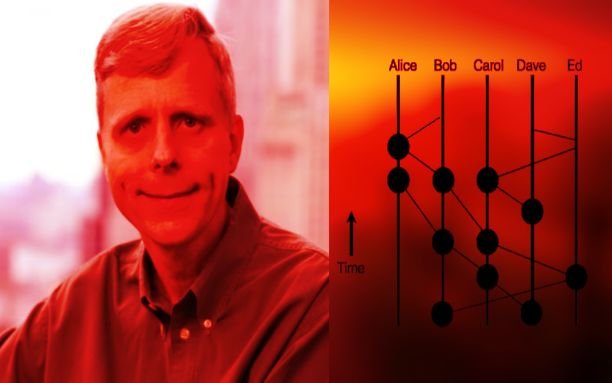
In 2016, a new distributed ledger technology named Hashgraph was introduced by the co-founder and CTO of Swirlds, Leemon Baird.
This technology can secure the network from different types of attacks by using its asynchronous Byzantine Fault Tolerance (aBFT) consensus algorithm.
It is mainly focussed on five fundamentals such as Performance, Security, Governance, Stability, and Regulatory Compliance.
Hashgraph technology found very useful and widely adopted as it has a great scope for scalability. But this technology still in the development phase.
Unfortunately, Hashgraph technology works in a centralized manner (limited private nodes network) so we can’t compare it with Blockchain technology which was developed by Satoshi Nakamoto in 2008 and blockchain is a decentralized public ledger (unlimited public nodes network).
Please keep in mind that blockchain and hashgraph both are different technology with different uses and goals, so don’t compare them together. Also, both scalability and security can’t be achieved together as if you want scalability then security will be a problem and if you want security then scalability will be a problem. So please don’t compare an apple with an orange.
In this article, we will cover the following topics:
- What is Hashgraph?
- How Hashgraph Works?
- Characteristics of Hashgraph
- Disadvantages of Hashgraph
- Applications of Hashgraph
- Conclusion
- Some important links for Hashgraph
1 What Is Hashgraph?

Hashgraph made up of two words “hash” and “graph” that shows it is a graphical representation of hashes.
Simply hashgraph is a Directed Acyclic Graph (DAG) that uses the concept of gossip about gossip protocol and virtual voting system.
It is also a distributed ledger technology but does not use the blocks like blockchain in order to stores information or data whereas it used gossip protocol with the timestamp and virtual voting that makes it very fast, secure, stable, and fair.
Hashgraph provides a high throughput of thousands of transactions per second which makes it more scalable and adaptable as compared to blockchain technology where bitcoin and ethereum can only handle 7 and 15 transactions per second.
The technology of hashgraph is still in the early stages of development but it can solve a lot of problems in the future.
The Hashgraph technology solves the Byzantine Generals’ Problem without using any costly consensus like Proof-of-Work(PoW) which is really a big achievement at all.
“What if anyone on Earth, at any moment, could just wave their hand and carve out a world of their own in cyberspace?”
– Co-Founder & Chief Scientist, DR. LEEMON BAIRD
2 How Hashgraph Works?
The step by step explanation of the working of hashgraph is shown below:
1. Normally, hashgraph is a directed acyclic graph where events containing transactions are recorded on it with timestamps and verified by a virtual voting system.
2. There are a number of privately running nodes that create the events by sending or broadcasting it to some other node randomly using the concept of the gossip protocol.
3. Every event contains the following information or data:
- all the transaction happened in that event
- the timestamp of that event occurred
- Hash of the event sender and the hash of the event receiver
4. Any node can create an event at any instant of time in order to share the data or information about the history and the current state of the network to other nodes randomly is referred here as gossiping of nodes.
5. There are no confirmations waiting from the other nodes of the network for an event created as required in blockchain, every event created is itself verified its validity by Virtual Voting instantly.
6. Each node that received an event of information is constantly shared this received information as well as the new information it has with other nodes randomly. This also protects the network from different types of malicious attacks.
7. Each node that received an event of information from an other node can easily verify the validity of received information by virtual voting as from the received information it can see that what the other nodes can see and know about current the network state and history past events. It makes the network more secure where it is impossible to fake the transactions and their orders.
Now let’s discuss the two main concepts that Hahsgraph consensus algorithm used which are shown below:
1.Gossip about Gossip
Hashgraph technology used the Gossip protocol in order to spread information on the network or for the communication of nodes in the network.
Nodes send the event containing data randomly to other nodes and those nodes who received the event will send it to the other nodes randomly and again those who received the event will do the same and it continues forever.
The events containing data spread on the network by nodes at the exponential rate on the network between the nodes by which almost all nodes get the latest state of the network at every instant as this process is very fast.
2. Virtual Voting
The Hashgraph consensus algorithm used the Virtual Voting technique in order to reach a consensus on the order of transactions.
As we know that hashgraph is made up of events that contained data and shared on the network between nodes. So these events are mainly divided into Rounds.
Each Round contains witnesses that are nothing but just a first event in a round for a given node. A node may have no witness in a round.
So all the witnesses in a round vote for the assumed famous witness in the previous round with yes or no by looking backward on the hashgraph that they have, where if one witness sees the famous witness by looking backward then it votes ‘yes’ otherwise it votes ‘no’. So if all the witnesses vote ‘yes’ then it means all the witnesses can see the famous witness by looking backward on the hashgraph, and hence it proves the assumed famous witness is really the famous witness. Finally, it provides the definitive order of transactions for the current round.
This is how Virtual Voting works.
3 Characteristics Of Hashgraph
Here are some important characteristics of the Hashgraph given below:
- Fast: Hashgraph uses a gossip protocol that makes it incredibly very fast with a very high throughput of thousands of transactions per second. It provides low-latency transactions where transaction can be broadcasted in just a few seconds.
- Secure: Hashgraph uses the asynchronous Byzantine fault-tolerant (ABFT) consensus algorithm with timestamps and a virtual voting system that provides it incredibly very powerful security where there is no chance for the DDoS and Sybil attacks.
- Fair: Hashgraph works in a fair way where we get fairness in the timestamps and transaction orders that can’t be manipulated by malicious nodes. It provides a fair access to information and events.
- Immutable: The transaction data on the hashgraph is irreversible and unchangeable. Every transaction that occurred on hashgraph is permanently recorded on it and can never be corrupted in any way.
- Stable: Run on a reliable network governed by term-limited enterprises with no authorized forks, and the ability to meet global data regulations.
- Distributed: It is distributed public ledger where everyone can access the data of the public ledger and this public ledger containing all the transaction data is distributed throughout the internet in the digital world.
- Low Cost: Hashgraph is using a gossip protocol that makes it very cheap to run the network at low cost and there is no high-cost consensus required in hashgraph like Proof of Work (PoW) and no mining at all.
- Scalable: Hashgraph has high throughput (thousands of transactions per second) and provides good security at a low cost. Also, it is very fast, stable and fair and can be used for micro-payments that make it more useful and more scalable than any other existing DLT technologies like blockchain.
4 Disadvantages of Hashgraph
Every good technology that has been developed in the world always face some issues and have some problems. There is no doubt that Hashgraph has a lot of benefits as it provides a lot of features and it is fast, secure, fair. So Hashgraph technology also has some problems given below:
- Private and Permissioned: The Hashgraph algorithm is patented by Leemon Baird which means it can only be used with the permission of its creator Leemon Baird that makes it a private property of him. It can be a big issue as he can influence the network and its development by controlling everything according to him that maybe for good actors or bad actors.
- Centralized Network: All the network nodes are private and in control of a party that governs the whole network and its developments. Also, they can forcefully run KYC and AML schemes in the hashgraph that is really a big problem in terms of privacy concerns.
5 Applications Of Hashgraph
There are a large number of applications of the Hashgraph as the hashgraph technology is fast, secure, fair, stable and more scalable. Some of them are shown below:
- Micro-Payments
- distributed capital markets
- Online Video Games
- live collaboration apps
- distributed MMOs
- StableCoin
- Banking
- Matching buyers and sellers on a stock market
- Real Estate
- Online Marketplace
- Edge Computing
- Auctions
- Dark Pools
- Patents
- Domain Names
- Cybersecure supply chain
- Instances where it matters who filed first
- Identity management
- pharmaceutical supply chains
- Tactical military intelligence for the Department of Defense (DOD)
- Secure power system transactive energy
6 Conclusion
Hashgraph is a new DLT (Distributed Ledger Technology) tech that is still in the development phase. It has a lot of space to grow as it is fair, secure and fast with a high throughput of thousands of transactions per second.
Also, hashgraph can only be used in private and permissioned environments as it is a patented algorithm by its creator.
Hashgraph network is totally controlled by a third party that can control the rights of the participants of the network and its developments, but the Hedera Hashgraph seems to create the public network of hashgraph that is totally open source for developers.
Some Important Links For Hashgraph
Hashgraph Official Website – click here
Hashgraph Whitepaper – click here
Dr. Leemon Baird Official Presentation on Hashgraph (recommended) – click here
Dr. Leemon Baird Youtube Guide (Hashgraph consensus working with Pictures) – click here
Github – click here